Pyhackthon 🐍🖥️
Introduction
👋 Hey Tech Enthusiasts and Cyber World Lovers!
Have you ever wondered how easy it is to evade antivirus software and code a fully functional malware tool? In today’s blog, we’ll dive deep into the world of Python and how script kiddies (those pesky noobs 😅) use it to develop harmful tools.
More importantly, you’ll learn how to build one yourself (for educational purposes, of course!) and how to defend yourself against them. ⚔️
Pyhackthon: Welcome to the Dark Side of Python 🌑
Python is a versatile, high-level programming language that is:
- Easy to Learn 💡
- Easy to Code 🛠️
- Full of Powerful Libraries 📚
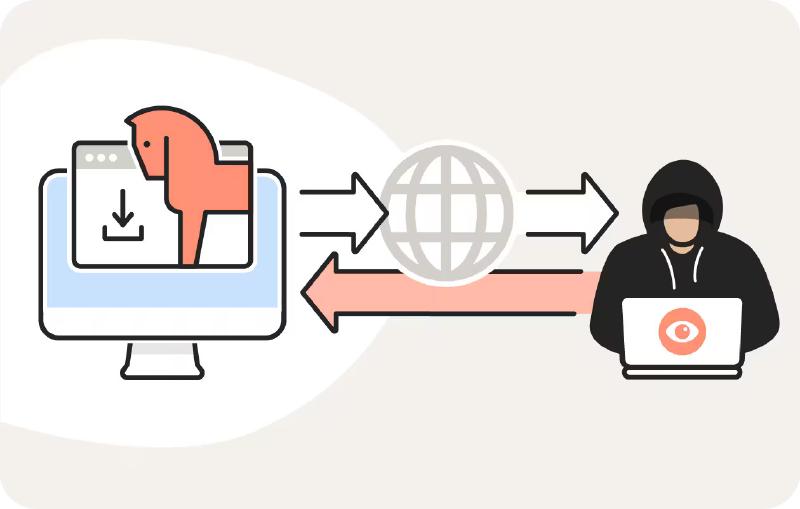
However, its flexibility has made it a favorite for cybercriminals too. They often misuse Python for creating malware that can harm systems. Today, we’re going to look into how a simple Python script can turn into a full-fledged Remote Access Trojan (RAT), and how you can protect yourself from such attacks.
RAT: The Dangerous Mouse 🐭💻
No, not that kind of rat! 🐀 In computer terms, RAT stands for Remote Access Trojan.
Imagine receiving a harmless-looking email attachment, and when you open it, someone gains complete control of your computer without your consent! 😱 Scary, right?
A RAT is like a fox disguised as Grandma 👵 (Trojan) but sneakier—giving attackers remote access to your system to steal data, monitor your activity, and even control your files.
Disclaimer 🛑:
Misusing this tool can land you in legal trouble—think late-night knock on the door kinda trouble 🚔. So, make sure you’re using it responsibly and ethically.
What Makes This Tool Special? 🎉
- Easy Setup - Get it running in minutes ⏲️
- No Port Forwarding Required - A hassle-free experience 🌐
- Accessible - All you need is an internet connection and a browser 🌍
🛠️ Setup and Installation 🛠️
Follow these simple steps:
- 🍴 Clone This Repository: Fork it, clone it, just get it!
- 📦 Install Requirements: Run the following command:
| |
- ✉️ Create a New Gmail Account: DO NOT use your personal account for this! Enter the credentials into
gmail.py.
🔓 Enable Less Secure Apps: Because we like living dangerously 😎.
📧 Configure Email: For receiving results and sending commands to
YOUR_MAIL.🖥️ Convert to Executable: Use
PyInstaller:
| |
- 💻 Install on the Target Machine: Insert evil laugh here 😈.
- ⏳ Wait 2 Minutes: Check your email for results.
- 🔧 Send Commands via Email: Flex those hacking muscles 💪.
- 🏁 Exit Command: Send the command
EXITto stop the tool. - 🎉 Congratulations! You’ve created your first Python RAT.
Aftermath 🎭
Once you’ve run the RAT, here’s what you can do:
- 🖥️ Run Some Commands.
- 🧠 Teach Others about cybersecurity risks.
- 💪 Contribute to improving this tool by adding features.
- 🌟 Star the Repo to show your support!
Prevention Tips 🚨
Now that you know how dangerous RATs can be, here’s how to protect yourself:
- Avoid clicking on suspicious links or opening unexpected attachments 🚫.
- Hover over links before clicking to see where they really lead 🔍.
- Always use antivirus software.
- Keep your system, browser, and antivirus up-to-date 🔄.
- Never download software from untrusted or pirated sources ❌.
Conclusion 🎯
So there you have it—the sneaky world of Remote Access Trojans. Always be cautious of what you click online. If something seems too good to be true, it probably is. When in doubt, ask a cyber professional.
Remember: just like your room, keep your online space locked and safe. 🛡️
Share your thoughts in the comments below and feel free to connect with me on GitHub, Instagram, or Telegram for more cool content!
Thank you for visiting my blog! 😁